Nginx + ModSecurity and OWASP CRS

This tutorial shows how to install ModSecurity (open source web application Firewall) in Nginx, and also enable the OWASP ModSecurity Core Rule Set (CRS).
Tested:
- Nginx Open Source 1.17.7
- ModSecurity 3.0
- OWASP ModSecurity CRS 3.2.2
- Debian
The official guide of installing ModSecurity for NGINX is very detail and well documented, and you should refer it. This guide is customized with my encountered problem and solution during the official Nginx + ModSecurity installation, just for self-reference and ease my future docker deployment.
Note
Assume Nginx is installed and configured at /etc/nginx, to install ModSecurity 3.0, Nginx 1.11.5 or later is required.
1. Install Prerequisite Packages.
1.2 We need the following packages to compile the ModSecurity and Nginx Connector source code on Ubuntu/Debian system. The required packages might be different for other Linux distributions like CentOS.
$ sudo apt install -y apt-utils autoconf automake build-essential git libcurl4-openssl-dev libgeoip-dev liblmdb-dev libpcre++-dev libtool libxml2-dev libyajl-dev pkgconf wget zlib1g-dev
Note
If you encounter any errors during this step, consider updating the system.
$ sudo apt update
2. Download and Compile ModSecurity 3.0
Download and compile the ModSecurity or libmodsecurity.
2.1 Clone the ModSecurity github repository.
$ pwd
/home/mkyong/download # any folder you like, we will download everything here
$ git clone --depth 1 -b v3/master --single-branch https://github.com/SpiderLabs/ModSecurity
$ ls -lsah
total 12K
4.0K drwxr-xr-x 3 mkyong mkyong 4.0K Jun 25 13:13 .
4.0K drwxr-xr-x 42 mkyong mkyong 4.0K Jun 25 13:11 ..
4.0K drwxr-xr-x 13 mkyong mkyong 4.0K Jun 25 13:13 ModSecurity
2.2 Change to the directory and compile the source code.
$ pwd
/home/mkyong/download
$ cd ModSecurity
$ git submodule init
$ git submodule update
$ ./build.sh
$ ./configure
# This takes time, 10 minutes or more depends on processing power.
$ make
# Install at /usr/local/modsecurity/
$ sudo make install
2.3 The last command make install copy ModSecurity’s files to /usr/local/modsecurity/.
$ cd /usr/local/modsecurity
/usr/local/modsecurity $ tree
.
├── bin
│ └── modsec-rules-check
├── include
│ └── modsecurity
│ ├── actions
│ │ └── action.h
│ ├── anchored_set_variable.h
│ ├── anchored_variable.h
│ ├── audit_log.h
│ ├── collection
│ │ ├── collection.h
│ │ └── collections.h
│ ├── debug_log.h
│ ├── intervention.h
│ ├── modsecurity.h
│ ├── reading_logs_via_rule_message.h
│ ├── rule.h
│ ├── rule_marker.h
│ ├── rule_message.h
│ ├── rules_exceptions.h
│ ├── rules.h
│ ├── rules_set.h
│ ├── rules_set_phases.h
│ ├── rules_set_properties.h
│ ├── rule_unconditional.h
│ ├── rule_with_actions.h
│ ├── rule_with_operator.h
│ ├── transaction.h
│ ├── variable_origin.h
│ └── variable_value.h
└── lib
├── libmodsecurity.a
├── libmodsecurity.la
├── libmodsecurity.so -> libmodsecurity.so.3.0.4
├── libmodsecurity.so.3 -> libmodsecurity.so.3.0.4
├── libmodsecurity.so.3.0.4
└── pkgconfig
└── modsecurity.pc
2.4 Some common errors and solutions.
Error 1
$ ./build.sh
./build.sh: 6: libtoolize: not found
./build.sh: 7: autoreconf: not found
./build.sh: 8: autoheader: not found
./build.sh: 9: automake: not found
./build.sh: 10: autoconf: not found
Please install the prerequisite packages to compile the source code.
Error 2
$ ./build.sh
libtoolize: putting auxiliary files in '.'.
libtoolize: copying file './ltmain.sh'
#...
fatal: No names found, cannot describe anything.
fatal: No names found, cannot describe anything.
#...
examples/multiprocess_c/Makefile.am: installing './depcomp'
configure.ac: installing './ylwrap'
fatal: No names found, cannot describe anything.
It’s safe to ignore the fatal messages fatal: No names found, cannot describe anything.
Error 3
$ make install
/usr/bin/mkdir -p '/usr/local/modsecurity/lib'
/usr/bin/mkdir: cannot create directory ‘/usr/local/modsecurity’: Permission denied
The make install need sudo or root access.
3. Download and Compile NGINX Connector for ModSecurity.
Download and compile the ModSecurity connector for Nginx as a dynamic module for Nginx.
3.1 Clone the ModSecurity connector repository.
$ pwd
/home/mkyong/download
$ git clone --depth 1 https://github.com/SpiderLabs/ModSecurity-nginx.git
3.2 We need the same running Nginx source code to compile the ModSecurity connector. Find the current version of the running Nginx server.
$ sudo nginx -v
nginx version: nginx/1.17.7
3.3 Download the Nginx source code.
$ pwd
/home/mkyong/download
$ wget http://nginx.org/download/nginx-1.17.7.tar.gz
$ tar zxvf nginx-1.17.7.tar.gz
3.4 Compile the module and copy the objs/ngx_http_modsecurity_module.so to /etc/nginx/modules.
$ pwd
/home/mkyong/download
ls -lsah
total 1.1M
4.0K drwxr-xr-x 5 mkyong mkyong 4.0K Jun 25 14:07 .
4.0K drwxr-xr-x 42 mkyong mkyong 4.0K Jun 25 13:11 ..
4.0K drwxr-xr-x 13 mkyong mkyong 4.0K Jun 25 13:20 ModSecurity
4.0K drwxr-xr-x 6 mkyong mkyong 4.0K Jun 25 13:59 ModSecurity-nginx
4.0K drwxr-xr-x 8 mkyong mkyong 4.0K Ogos 13 2019 nginx-1.17.7
1012K -rw-r--r-- 1 mkyong mkyong 1009K Ogos 14 2019 nginx-1.17.7.tar.gz
$ cd nginx-1.17.7
$ ./configure --with-compat --add-dynamic-module=../ModSecurity-nginx
$ make modules
$ sudo cp objs/ngx_http_modsecurity_module.so /etc/nginx/modules/
3.5 Some common errors and solutions.
Error 1
$ sudo cp objs/ngx_http_modsecurity_module.so /etc/nginx/modules/
cp: cannot create regular file '/etc/nginx/modules/': Not a directory
$ sudo mkdir /etc/nginx/modules/
$ sudo cp objs/ngx_http_modsecurity_module.so /etc/nginx/modules/
The folder /etc/nginx/modules/ doesn’t exist, and please create the folder before the copy command.
4. Load the Nginx ModSecurity Connector.
4.1 Edit the /etc/nginx/nginx.conf, and loads the ngx_http_modsecurity_module.so at the top level context.
$ sudo vim /etc/nginx/nginx.conf
user www-data;
worker_processes auto;
pid /run/nginx.pid;
## Nginx ModSecurity Connector
load_module modules/ngx_http_modsecurity_module.so;
events {
worker_connections 1024;
}
http {
## omitted...
include /etc/nginx/conf.d/*.conf;
}
4.2 Verify if everything is ok.
$ sudo service nginx configtest
nginx: the configuration file /etc/nginx/nginx.conf syntax is ok
nginx: configuration file /etc/nginx/nginx.conf test is successful
Note
If the test configuration is failed, please find the error description inside the standard Nginx log file, normally, /var/log/nginx/error.log.
4.3 Some common errors and solutions.
Error 1
The load_module directive is specified too late in /etc/nginx/nginx.conf.
user www-data;
worker_processes auto;
pid /run/nginx.pid;
events {
worker_connections 1024;
}
# directive is specified too late
load_module modules/ngx_http_modsecurity_module.so;
Move the load_module above the event should solve this.
user www-data;
worker_processes auto;
pid /run/nginx.pid;
# move here
load_module modules/ngx_http_modsecurity_module.so;
events {
worker_connections 1024;
}
Error 2
The modules relative path points to another directory?
dlopen() "/usr/share/nginx/modules/ngx_http_modsecurity_module.so" failed
(/usr/share/nginx/modules/ngx_http_modsecurity_module.so:
cannot open shared object file: No such file or directory) in /etc/nginx/nginx.conf:6
To solve it, hard code the physical path /etc/nginx/modules/.
user www-data;
worker_processes auto;
pid /run/nginx.pid;
# hard code the path.
load_module /etc/nginx/modules/ngx_http_modsecurity_module.so;
events {
worker_connections 1024;
}
5. Nginx + ModSecurity Configuration Files.
5.1 Create a new folder /etc/nginx/modsec, and puts all the ModSecurity configuration files here.
$ sudo mkdir /etc/nginx/modsec
5.2 Download the recommended ModSecurity configuration file, and renamed it to modsecurity.conf
$ cd /etc/nginx/modsec
$ sudo wget https://raw.githubusercontent.com/SpiderLabs/ModSecurity/v3/master/modsecurity.conf-recommended
$ sudo mv modsecurity.conf-recommended modsecurity.conf
5.3 Edit the modsecurity.conf, and change the default SecRuleEngine DetectionOnly to SecRuleEngine On.
$ pwd
/etc/nginx/modsec
# vim or nano or text editor
$ sudo vim modsecurity.conf
# -- Rule engine initialization ----------------------------------------------
# Enable ModSecurity, attaching it to every transaction. Use detection
# only to start with, because that minimises the chances of post-installation
# disruption.
#
# SecRuleEngine DetectionOnly
SecRuleEngine On
5.4 Create a new ModSecurity’s configuration file /etc/nginx/modsec/main.conf.
$ sudo vim /etc/nginx/modsec/main.conf
Later we will include the OWASP core rule set here.
# Include the recommended configuration
Include /etc/nginx/modsec/modsecurity.conf
# Other ModSecurity Rules
5.5 In the main Nginx conf file, server context, turn on the modsecurity for the specific server.
server {
# ...
modsecurity on;
modsecurity_rules_file /etc/nginx/modsec/main.conf;
}
5.6 Copy the unicode.mapping to /etc/nginx/modsec/unicode.mapping, it is inside the (step 1) ModSecurity’s source code.
$ pwd
/home/mkyong/download
ls -lsah
total 1.1M
4.0K drwxr-xr-x 5 mkyong mkyong 4.0K Jun 25 14:07 .
4.0K drwxr-xr-x 42 mkyong mkyong 4.0K Jun 25 15:45 ..
4.0K drwxr-xr-x 13 mkyong mkyong 4.0K Jun 25 13:20 ModSecurity
4.0K drwxr-xr-x 6 mkyong mkyong 4.0K Jun 25 13:59 ModSecurity-nginx
4.0K drwxr-xr-x 9 mkyong mkyong 4.0K Jun 25 14:08 nginx-1.16.1
1012K -rw-r--r-- 1 mkyong mkyong 1009K Ogos 14 2019 nginx-1.16.1.tar.gz
$ sudo cp ModSecurity/unicode.mapping /etc/nginx/modsec/
The official Nginx + ModSecurity installation guide didn’t mention about this. However, failed to find the unicode.mapping will hit the following error message during Nginx reload.
020/06/25 15:46:56 [emerg] 21585#21585: "modsecurity_rules_file" directive Rules error.
File: /etc/nginx/modsec/modsecurity.conf. Line: 237. Column: 17.
Failed to locate the unicode map file from: unicode.mapping Looking at:
'unicode.mapping',
'unicode.mapping',
'/etc/nginx/modsec/unicode.mapping',
'/etc/nginx/modsec/unicode.mapping'.
in /etc/nginx/sites-enabled/default:26
5.7 The last step, always verifies if everything is ok.
$ sudo service nginx configtest
6. OWASP ModSecurity Core Rule Set
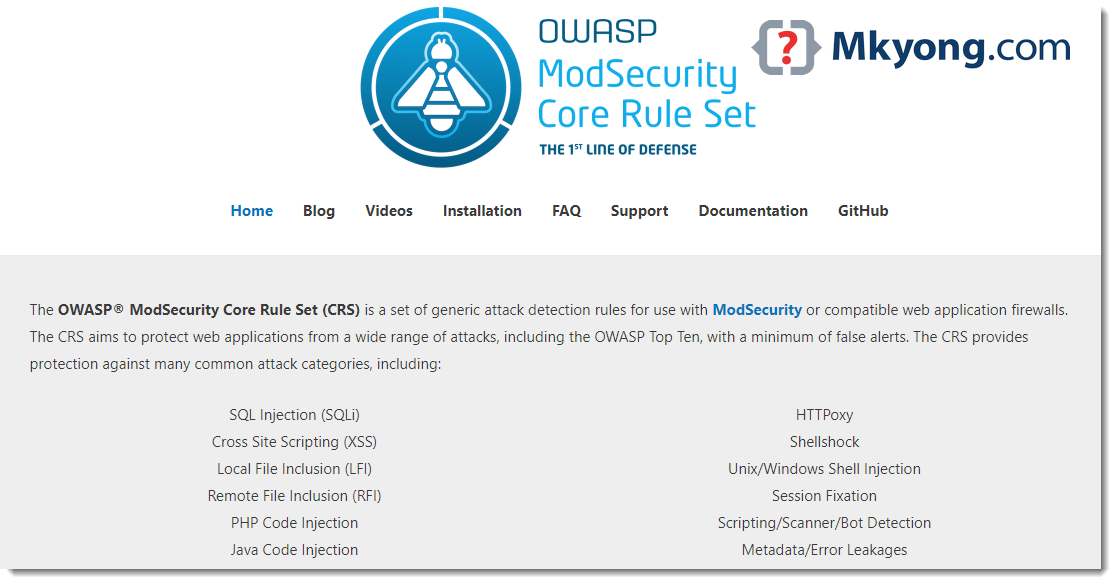
The ModSecurity rules are empty now, and we need at least enable the OWASP Core Rule Set (CRS) to protect some general attacks (SQLi, XSS, LFI, and etc), bots, and scanners.
6.1 Download the OWASP core rule set.
$ pwd
/home/mkyong/download
$ wget https://github.com/coreruleset/coreruleset/archive/v3.2.0.tar.gz
# compare the checksum
$ sha1sum v3.2.0.tar.gz
f54dae40709af1decec0e9c91e0aab4e25542742 v3.2.0.tar.gz
$ tar zxvf v3.2.0.tar.gz
$ cd coreruleset-3.2.0
$ ls -lsah
total 184K
4.0K drwxr-xr-x 6 mkyong mkyong 4.0K Sep 24 2019 .
4.0K drwxr-xr-x 6 mkyong mkyong 4.0K Jun 25 16:04 ..
64K -rw-r--r-- 1 mkyong mkyong 62K Sep 24 2019 CHANGES
8.0K -rw-r--r-- 1 mkyong mkyong 7.7K Sep 24 2019 CONTRIBUTING.md
4.0K -rw-r--r-- 1 mkyong mkyong 2.8K Sep 24 2019 CONTRIBUTORS.md
32K -rw-r--r-- 1 mkyong mkyong 31K Sep 24 2019 crs-setup.conf.example
4.0K drwxr-xr-x 3 mkyong mkyong 4.0K Sep 24 2019 documentation
4.0K drwxr-xr-x 2 mkyong mkyong 4.0K Sep 24 2019 .github
4.0K -rw-r--r-- 1 mkyong mkyong 374 Sep 24 2019 .gitignore
4.0K -rw-r--r-- 1 mkyong mkyong 176 Sep 24 2019 .gitmodules
20K -rw-r--r-- 1 mkyong mkyong 17K Sep 24 2019 INSTALL
4.0K -rw-r--r-- 1 mkyong mkyong 2.8K Sep 24 2019 KNOWN_BUGS
12K -rw-r--r-- 1 mkyong mkyong 12K Sep 24 2019 LICENSE
4.0K -rw-r--r-- 1 mkyong mkyong 2.3K Sep 24 2019 README.md
4.0K drwxr-xr-x 2 mkyong mkyong 4.0K Sep 24 2019 rules ## Rules here
4.0K -rw-r--r-- 1 mkyong mkyong 2.1K Sep 24 2019 .travis.yml
4.0K drwxr-xr-x 13 mkyong mkyong 4.0K Sep 24 2019 util
6.2 Moves the OWASP CRS folder coreruleset-3.2.0 to /usr/local
$ cd ..
$ pwd
/home/mkyong/download
$ sudo mv coreruleset-3.2.0 /usr/local
$ ls -lsah /usr/local
total 48K
4.0K drwxr-xr-x 12 root root 4.0K Jun 25 16:08 .
4.0K drwxr-xr-x 14 root root 4.0K Okt 17 2019 ..
4.0K drwxr-xr-x 6 mkyong mkyong 4.0K Sep 24 2019 coreruleset-3.2.0
4.0K drwxr-xr-x 5 root root 4.0K Jun 25 13:28 modsecurity
#...
6.3 The ownership is changed after the move; it is better to change the ownership to root.
$ sudo chown root:root -R /usr/local/coreruleset-3.2.0
$ ls -lsah /usr/local
total 48K
4.0K drwxr-xr-x 12 root root 4.0K Jun 25 16:08 .
4.0K drwxr-xr-x 14 root root 4.0K Okt 17 2019 ..
4.0K drwxr-xr-x 6 root root 4.0K Sep 24 2019 coreruleset-3.2.0
4.0K drwxr-xr-x 5 root root 4.0K Jun 25 13:28 modsecurity
#...
6.4 Create a new crs-setup.conf as a copy of crs-setup.conf.example.
$ cd /usr/local/coreruleset-3.2.0
$ sudo cp crs-setup.conf.example crs-setup.conf
6.5 Include the crs-setup.conf and rule/* in the main ModSecurity configuration file /etc/nginx/modsec/main.conf.
$ sudo vim /etc/nginx/modsec/main.conf
# Include the recommended configuration
Include /etc/nginx/modsec/modsecurity.conf
# OWASP CRS v3.2.0 rules
Include /usr/local/coreruleset-3.2.0/crs-setup.conf
# This will include all the rules, need filter later
Include /usr/local/coreruleset-3.2.0/rules/*.conf
6.6 Make sure everything is ok, and reload the Nginx. Now, the OWASP rules are enabled in ModSecurity.
$ sudo service nginx configtest
$ sudo service nginx reload
6.7 By default, the OWASP rule REQUEST-913-SCANNER-DETECTION.conf, and it’s data scanners-user-agents.data defined the user agent Nikto as blocked, a simple curl should return a 403 error.
$ curl -H "User-Agent: Nikto" http://localhost/
<html>
<head><title>403 Forbidden</title></head>
<body>
<center><h1>403 Forbidden</h1></center>
<hr><center>nginx</center>
</body>
</html>
Done. Everything is working now.
6.8 Review the OWASP core set rules:
$ ls -lsa /usr/local/coreruleset-3.2.0/rules
-rw-r--r-- 1 root root 738 Sep 24 2019 crawlers-user-agents.data
-rw-r--r-- 1 root root 551 Sep 24 2019 iis-errors.data
-rw-r--r-- 1 root root 933 Sep 24 2019 java-classes.data
-rw-r--r-- 1 root root 264 Sep 24 2019 java-code-leakages.data
-rw-r--r-- 1 root root 240 Sep 24 2019 java-errors.data
-rw-r--r-- 1 root root 31208 Sep 24 2019 lfi-os-files.data
-rw-r--r-- 1 root root 5409 Sep 24 2019 php-config-directives.data
-rw-r--r-- 1 root root 9201 Sep 24 2019 php-errors.data
-rw-r--r-- 1 root root 683 Sep 24 2019 php-function-names-933150.data
-rw-r--r-- 1 root root 21282 Sep 24 2019 php-function-names-933151.data
-rw-r--r-- 1 root root 224 Sep 24 2019 php-variables.data
-rw-r--r-- 1 root root 7588 Sep 24 2019 REQUEST-900-EXCLUSION-RULES-BEFORE-CRS.conf.example
-rw-r--r-- 1 root root 12580 Sep 24 2019 REQUEST-901-INITIALIZATION.conf
-rw-r--r-- 1 root root 12369 Sep 24 2019 REQUEST-903.9001-DRUPAL-EXCLUSION-RULES.conf
-rw-r--r-- 1 root root 23286 Sep 24 2019 REQUEST-903.9002-WORDPRESS-EXCLUSION-RULES.conf
-rw-r--r-- 1 root root 9074 Sep 24 2019 REQUEST-903.9003-NEXTCLOUD-EXCLUSION-RULES.conf
-rw-r--r-- 1 root root 7515 Sep 24 2019 REQUEST-903.9004-DOKUWIKI-EXCLUSION-RULES.conf
-rw-r--r-- 1 root root 1792 Sep 24 2019 REQUEST-903.9005-CPANEL-EXCLUSION-RULES.conf
-rw-r--r-- 1 root root 16029 Sep 24 2019 REQUEST-903.9006-XENFORO-EXCLUSION-RULES.conf
-rw-r--r-- 1 root root 1499 Sep 24 2019 REQUEST-905-COMMON-EXCEPTIONS.conf
-rw-r--r-- 1 root root 9696 Sep 24 2019 REQUEST-910-IP-REPUTATION.conf
-rw-r--r-- 1 root root 2681 Sep 24 2019 REQUEST-911-METHOD-ENFORCEMENT.conf
-rw-r--r-- 1 root root 9861 Sep 24 2019 REQUEST-912-DOS-PROTECTION.conf
-rw-r--r-- 1 root root 7296 Sep 24 2019 REQUEST-913-SCANNER-DETECTION.conf
-rw-r--r-- 1 root root 47283 Sep 24 2019 REQUEST-920-PROTOCOL-ENFORCEMENT.conf
-rw-r--r-- 1 root root 10968 Sep 24 2019 REQUEST-921-PROTOCOL-ATTACK.conf
-rw-r--r-- 1 root root 6018 Sep 24 2019 REQUEST-930-APPLICATION-ATTACK-LFI.conf
-rw-r--r-- 1 root root 5594 Sep 24 2019 REQUEST-931-APPLICATION-ATTACK-RFI.conf
-rw-r--r-- 1 root root 53969 Sep 24 2019 REQUEST-932-APPLICATION-ATTACK-RCE.conf
-rw-r--r-- 1 root root 33006 Sep 24 2019 REQUEST-933-APPLICATION-ATTACK-PHP.conf
-rw-r--r-- 1 root root 3923 Sep 24 2019 REQUEST-934-APPLICATION-ATTACK-NODEJS.conf
-rw-r--r-- 1 root root 43325 Sep 24 2019 REQUEST-941-APPLICATION-ATTACK-XSS.conf
-rw-r--r-- 1 root root 74837 Sep 24 2019 REQUEST-942-APPLICATION-ATTACK-SQLI.conf
-rw-r--r-- 1 root root 5300 Sep 24 2019 REQUEST-943-APPLICATION-ATTACK-SESSION-FIXATION.conf
-rw-r--r-- 1 root root 15934 Sep 24 2019 REQUEST-944-APPLICATION-ATTACK-JAVA.conf
-rw-r--r-- 1 root root 4039 Sep 24 2019 REQUEST-949-BLOCKING-EVALUATION.conf
-rw-r--r-- 1 root root 4802 Sep 24 2019 RESPONSE-950-DATA-LEAKAGES.conf
-rw-r--r-- 1 root root 17749 Sep 24 2019 RESPONSE-951-DATA-LEAKAGES-SQL.conf
-rw-r--r-- 1 root root 3594 Sep 24 2019 RESPONSE-952-DATA-LEAKAGES-JAVA.conf
-rw-r--r-- 1 root root 5072 Sep 24 2019 RESPONSE-953-DATA-LEAKAGES-PHP.conf
-rw-r--r-- 1 root root 5727 Sep 24 2019 RESPONSE-954-DATA-LEAKAGES-IIS.conf
-rw-r--r-- 1 root root 4179 Sep 24 2019 RESPONSE-959-BLOCKING-EVALUATION.conf
-rw-r--r-- 1 root root 6577 Sep 24 2019 RESPONSE-980-CORRELATION.conf
-rw-r--r-- 1 root root 3001 Sep 24 2019 RESPONSE-999-EXCLUSION-RULES-AFTER-CRS.conf.example
-rw-r--r-- 1 root root 2043 Sep 24 2019 restricted-files.data
-rw-r--r-- 1 root root 390 Sep 24 2019 restricted-upload.data
-rw-r--r-- 1 root root 216 Sep 24 2019 scanners-headers.data
-rw-r--r-- 1 root root 418 Sep 24 2019 scanners-urls.data
-rw-r--r-- 1 root root 4571 Sep 24 2019 scanners-user-agents.data
-rw-r--r-- 1 root root 717 Sep 24 2019 scripting-user-agents.data
-rw-r--r-- 1 root root 1894 Sep 24 2019 sql-errors.data
-rw-r--r-- 1 root root 1380 Sep 24 2019 unix-shell.data
-rw-r--r-- 1 root root 3920 Sep 24 2019 windows-powershell-commands.data
Many 903 EXCLUSION rules target for specified platforms to avoid false positive. For examples, to enable the WordPress exclusion rule REQUEST-903.9002-WORDPRESS-EXCLUSION-RULES.conf, we need to uncomment the rule id 900130, and defined the tx.crs_exclusions_wordpress=1 in crs-setup.conf file manually, otherwise many false positive will fire at WordPress’s login, admin, and post pages.
$ cd /usr/local/coreruleset-3.2.0
$ sudo vim crs-setup.conf
# -- [[ Application Specific Rule Exclusions ]] ----------------------------------------
#
# To use this functionality you must specify a supported application. To do so
# uncomment rule 900130. In addition to uncommenting the rule you will need to
# specify which application(s) you'd like to enable exclusions for. Only a
# (very) limited set of applications are currently supported, please use the
# filenames prefixed with 'REQUEST-903' to guide you in your selection.
# Such filenames use the following convention:
# REQUEST-903.9XXX-{APPNAME}-EXCLUSIONS-RULES.conf
#
# ...
#
SecAction \
"id:900130,\
phase:1,\
nolog,\
pass,\
t:none,\
setvar:tx.crs_exclusions_wordpress=1"
# setvar:tx.crs_exclusions_cpanel=1,\
# setvar:tx.crs_exclusions_drupal=1,\
# setvar:tx.crs_exclusions_dokuwiki=1,\
# setvar:tx.crs_exclusions_nextcloud=1,\
# setvar:tx.crs_exclusions_wordpress=1,\
# setvar:tx.crs_exclusions_xenforo=1"
6.9 If the system uses only PHP, it feels safe to move or delete the non-related rules like Java and Node.
-rw-r--r-- 1 root root 33006 Sep 24 2019 REQUEST-933-APPLICATION-ATTACK-PHP.conf
# no need this
-rw-r--r-- 1 root root 3923 Sep 24 2019 REQUEST-934-APPLICATION-ATTACK-NODEJS.conf
-rw-r--r-- 1 root root 15934 Sep 24 2019 REQUEST-944-APPLICATION-ATTACK-JAVA.conf
7. Nginx ModSecurity Logging
After integrated Nginx and ModSecurity, by default, the errors will go Nginx’s error log /var/log/nginx/error.log and ModSecurity audit log /var/log/modsec_audit.log.
Note
The ModSecurity audit log modsec_audit.log contains detailed information about the malicious requests, but the log file size will increase extremely fast, remember to turn it off in production server.
To disable the ModSecurity’s audit logging, edit modsecurity.conf and change the value from SecAuditEngine RelevantOnly to SecAuditEngine off.
$ sudo vim /etc/nginx/modsec/modsecurity.conf
Scroll to the end of the file, we should find Audit log configuration
# -- Audit log configuration -------------------------------------------------
# Log the transactions that are marked by a rule, as well as those that
# trigger a server error (determined by a 5xx or 4xx, excluding 404,
# level response status codes).
#
# SecAuditEngine RelevantOnly
# SecAuditLogRelevantStatus "^(?:5|4(?!04))"
SecAuditEngine off
Further Reading
Please refer to this official ModSecurity: Logging and Debugging.
Great guide. Thank You!
Hey, thanks for your manual it was a welcome addition to the official manual. When I do curl -H “User-Agent: Nikto” http://myservername/ I get the 301 page as expected, but when I do curl -H “User-Agent: Nikto” https://myservername/ (so with https instead of http) I get a normal website as a result.
Is this supposed to be that way? How do I get modsecurity to also block on https?
When error:
nginx -t
nginx: [emerg] module “/usr/share/nginx/modules/ngx_http_modsecurity_module.so” is not binary compatible in /etc/nginx/modules-enabled/51-mod-http-modsecurity.conf:1
nginx: configuration file /etc/nginx/nginx.conf test failed
Drop the –with-compat option: https://serverfault.com/questions/988250/nginx-module-not-binary-compatible-after-compilation-on-centos-7
Hello, good afternoon, I did everything to be able to release wordpress, but wp-admin keeps blocking. What should I do?